Flare-On
Flare-On is a reverse engineering CTF ran formerly ran by Mandiant (now part of Google). It has been running since 2014 annually.
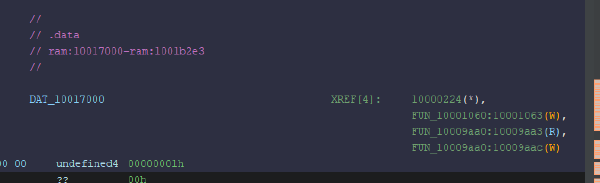
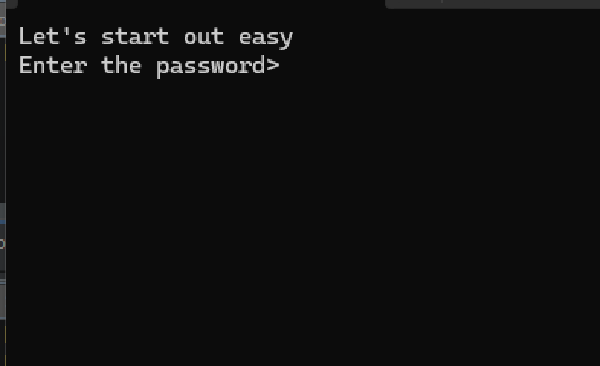
The process is simple, start at challenge 1, find the flag (which always fits the format <flag>@flare-on.com). When you input the flag correctly, it will unlock challenge 2 etc. Note that the challenges get arguably tougher.
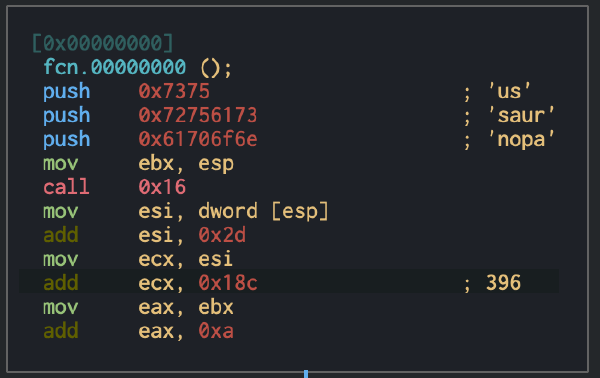
This challenge is much more than basic reversing and string grepping. I’ve solved a few dozen of these in my spare time and they cover a large theme of challenges such as mildly different versions of known malicious techniques, encryption mechanisms and of course lots and lots of memes.
I can tell you for a fact that working through these challenges will make you a great reverse engineer but it is extremely tough and a major time sink. The glory of beating the challenge however is immeasurable.
I’m working my way through the challenges, so below is the current status of my progress. Click on completed icons to see my report.
| 01 | 02 | 03 | 04 | 05 | 06 | 07 | 08 | 09 | 10 | 11 | |
|---|---|---|---|---|---|---|---|---|---|---|---|
| FlareOn 01 (5/7) | ✅ | ✅ | ✅ | ✅ | ✅ | ❌ | ❌ | ||||
| FlareOn 02 (1/11) | ✅ | ❌ | ❌ | ❌ | ❌ | ❌ | ❌ | ❌ | ❌ | ❌ | ❌ |
2026